Create the control
What are we going to do?
We are going to perform the following steps:
- define another product with a version and add it to the existing cloud-engineering-governance portfolio
- add the source code for our product
- provision that product into a spoke account
Step by step guide
Here are the steps you need to follow to “Create the control”
Define a product with a version and a portfolio
-
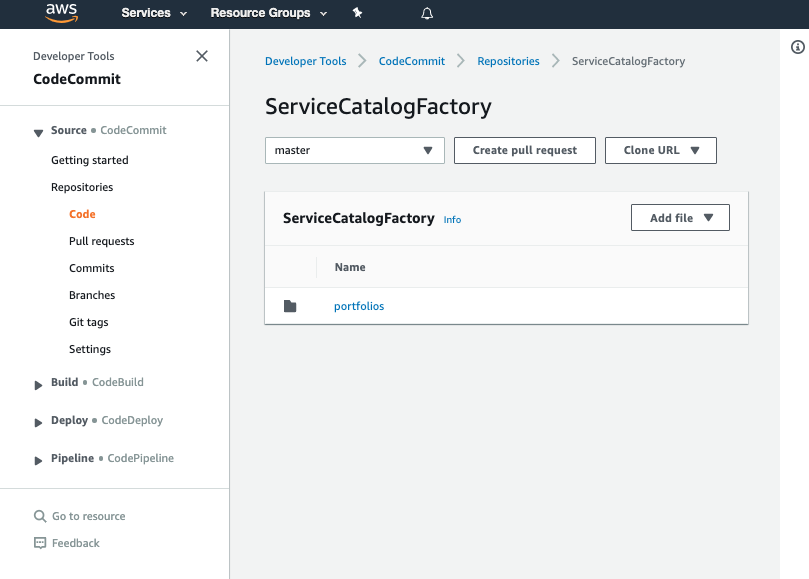
Navigate to the ServiceCatalogFactory CodeCommit repository again
-
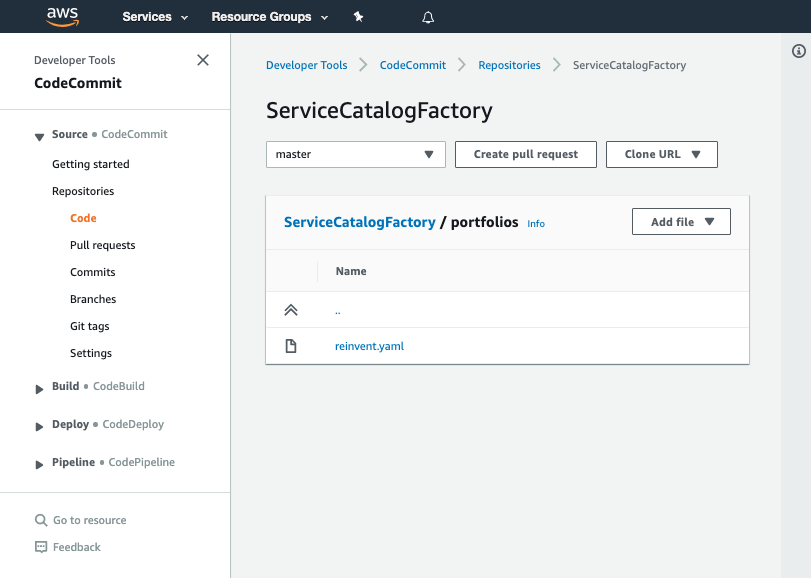
Click on portfolios
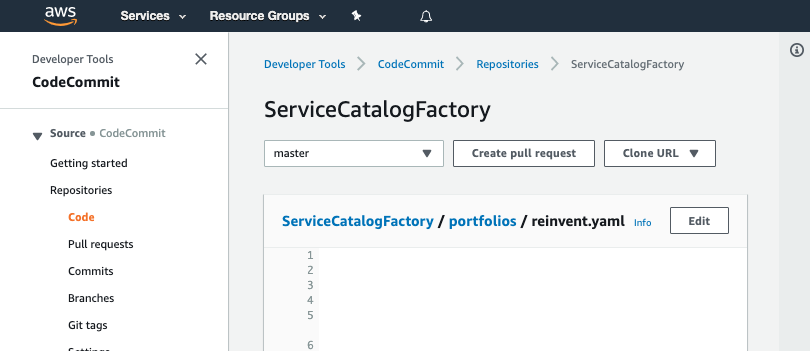
- Click on reinvent.yaml
- Click Edit
- We will need to insert the following to the products section:
- Name: "aws-config-rds-storage-encrypted"
Owner: "data-governance@example.com"
Description: "Enables AWS Config rule - aws-config-rds-storage-encrypted"
Distributor: "cloud-engineering"
SupportDescription: "Speak to data-governance@example.com about exceptions and speak to cloud-engineering@example.com about implementation issues"
SupportEmail: "cloud-engineering@example.com"
SupportUrl: "https://wiki.example.com/cloud-engineering/data-governance/aws-config-rds-storage-encrypted"
Tags:
- Key: "type"
Value: "governance"
- Key: "creator"
Value: "cloud-engineering"
- Key: "cost-center"
Value: "governance"
Versions:
- Name: "v1"
Description: "v1 of aws-config-rds-storage-encrypted"
Active: True
Source:
Provider: "CodeCommit"
Configuration:
RepositoryName: "aws-config-rds-storage-encrypted"
BranchName: "main"
Portfolios:
- "cloud-engineering-governance"
- Once completed it should like look this:
Schema: factory-2019-04-01
Products:
- Name: "aws-config-desired-instance-types"
Owner: "budget-and-cost-governance@example.com"
Description: "Enables AWS Config rule - desired-instance-type with our RIs"
Distributor: "cloud-engineering"
SupportDescription: "Speak to budget-and-cost-governance@example.com about exceptions and speak to cloud-engineering@example.com about implementation issues"
SupportEmail: "cloud-engineering@example.com"
SupportUrl: "https://wiki.example.com/cloud-engineering/budget-and-cost-governance/aws-config-desired-instance-types"
Tags:
- Key: "type"
Value: "governance"
- Key: "creator"
Value: "cloud-engineering"
- Key: "cost-center"
Value: "governance"
Versions:
- Name: "v1"
Description: "v1 of aws-config-desired-instance-types"
Active: True
Source:
Provider: "CodeCommit"
Configuration:
RepositoryName: "aws-config-desired-instance-types"
BranchName: "main"
Portfolios:
- "cloud-engineering-governance"
- Name: "aws-config-rds-storage-encrypted"
Owner: "data-governance@example.com"
Description: "Enables AWS Config rule - aws-config-rds-storage-encrypted"
Distributor: "cloud-engineering"
SupportDescription: "Speak to data-governance@example.com about exceptions and speak to cloud-engineering@example.com about implementation issues"
SupportEmail: "cloud-engineering@example.com"
SupportUrl: "https://wiki.example.com/cloud-engineering/data-governance/aws-config-rds-storage-encrypted"
Tags:
- Key: "type"
Value: "governance"
- Key: "creator"
Value: "cloud-engineering"
- Key: "cost-center"
Value: "governance"
Versions:
- Name: "v1"
Description: "v1 of aws-config-rds-storage-encrypted"
Active: True
Source:
Provider: "CodeCommit"
Configuration:
RepositoryName: "aws-config-rds-storage-encrypted"
BranchName: "main"
Portfolios:
- "cloud-engineering-governance"
Portfolios:
- DisplayName: "cloud-engineering-governance"
Description: "Portfolio containing the products needed to govern AWS accounts"
ProviderName: "cloud-engineering"
Associations:
- "arn:aws:iam::${AWS::AccountId}:role/TeamRole"
Tags:
- Key: "type"
Value: "governance"
- Key: "creator"
Value: "cloud-engineering"
- Key: "cost-center"
Value: "governance"
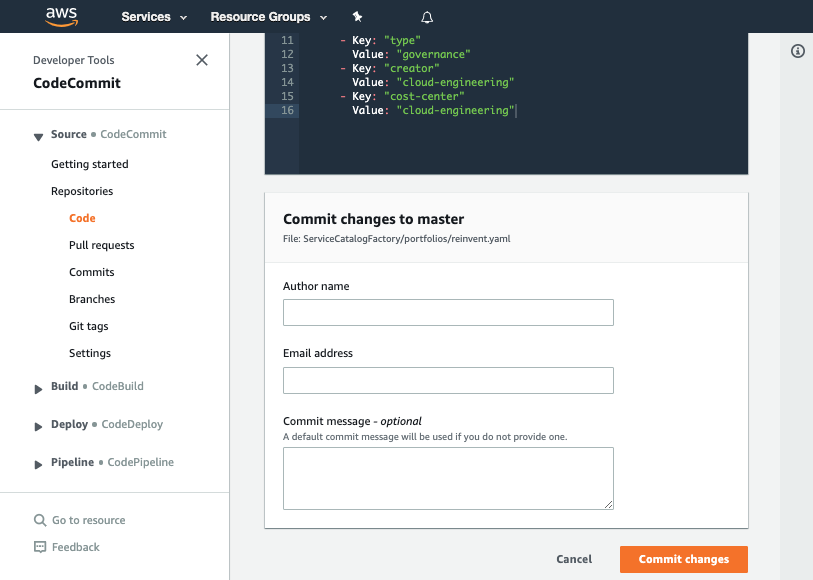
- Set your Author name
- Set your Email address
- Set your Commit message
Using a good / unique commit message will help you understand what is going on later.
- Click the Commit changes button:
What did we just do?
The YAML we pasted in the previous step told the framework to perform several actions:
- create a product named aws-config-rds-storage-encrypted
- add a v1 of our product
- add the product: aws-config-rds-storage-encrypted to the portfolio: cloud-engineering-governance
Verify that the change worked
Once you have made your changes the ServiceCatalogFactory Pipeline should have run. If you were very quick, the pipeline may still be running. If it has not yet started feel free to the hit the Release change button.
Once it has completed it should show the Source and Build stages in green to indicate they have completed successfully:
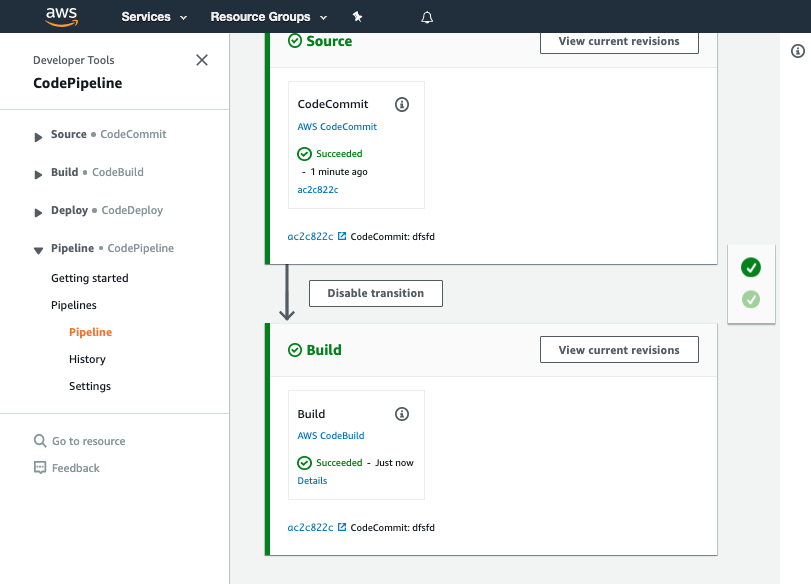
If this is failing please raise your hand for some assistance
Add the source code for our product
When you configured your product version, you specified the following version:
Versions:
- Name: "v1"
Description: "v1 of aws-config-rds-storage-encrypted"
Active: True
Source:
Provider: "CodeCommit"
Configuration:
RepositoryName: "aws-config-rds-storage-encrypted"
BranchName: "main"
This tells the framework the source code for the product comes from the main branch of a CodeCommit repository of the name aws-config-rds-storage-encrypted.
We now need to create the CodeCommit repository and add the CloudFormation template we are going to use for our product.
-
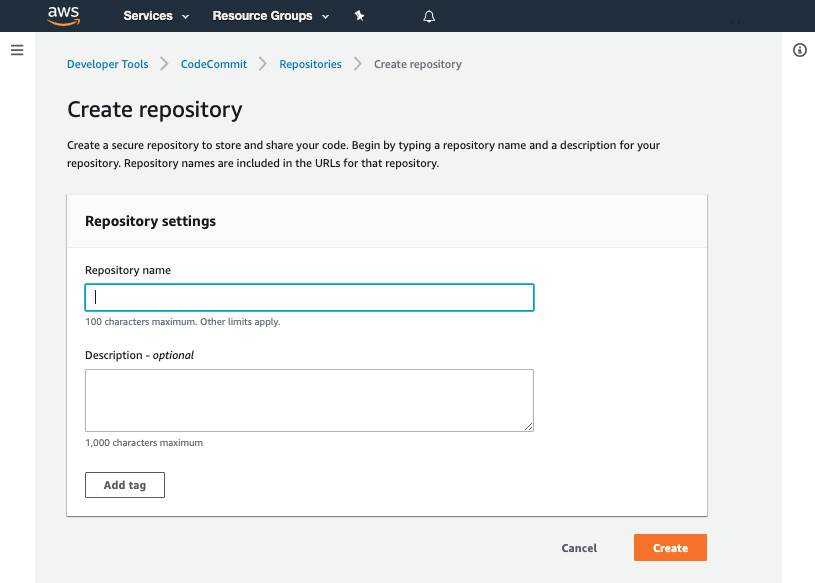
Navigate to AWS CodeCommit
-
Click Create repository
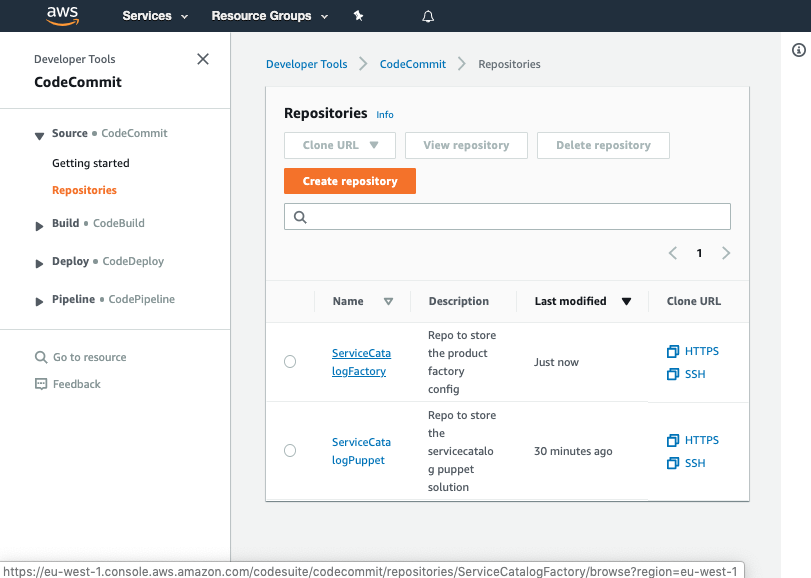
- Input the name
aws-config-rds-storage-encrypted
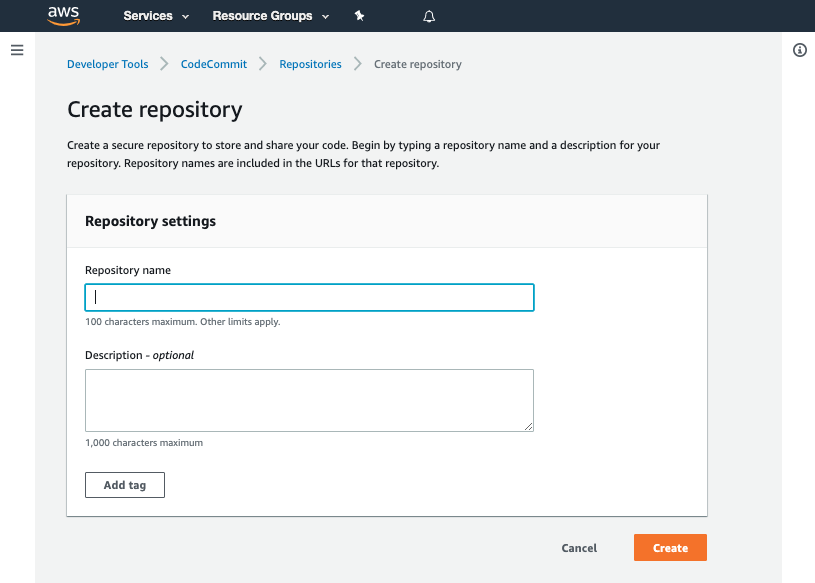
- Click Create
- Scroll down to the bottom of the page and hit the Create file button
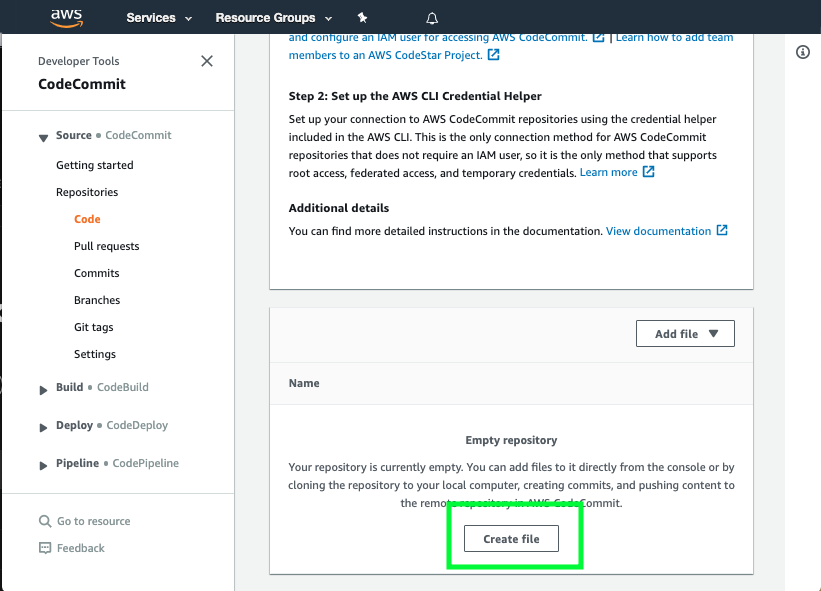
- Copy the following snippet into the main input field:
AWSTemplateFormatVersion: '2010-09-09'
Description: "Create an AWS Config rule ensuring RDS instances use encrypted storage"
Resources:
AWSConfigRule:
Type: AWS::Config::ConfigRule
Properties:
ConfigRuleName: "rds-storage-encrypted"
Description: "Checks whether storage encryption is enabled for your RDS DB instances."
Scope:
ComplianceResourceTypes:
- "AWS::RDS::DBInstance"
Source:
Owner: AWS
SourceIdentifier: RDS_STORAGE_ENCRYPTED
-
Set the File name to
product.template.yaml -
Set your Author name
-
Set your Email address
-
Set your Commit message
Using a good / unique commit message will help you understand what is going on later.
Creating that file should trigger your aws-config-rds-storage-encrypted-v1-pipeline.
Once the pipeline has completed it should show the Source, Package, Package and Deploy stages in green to indicate they have completed successfully:
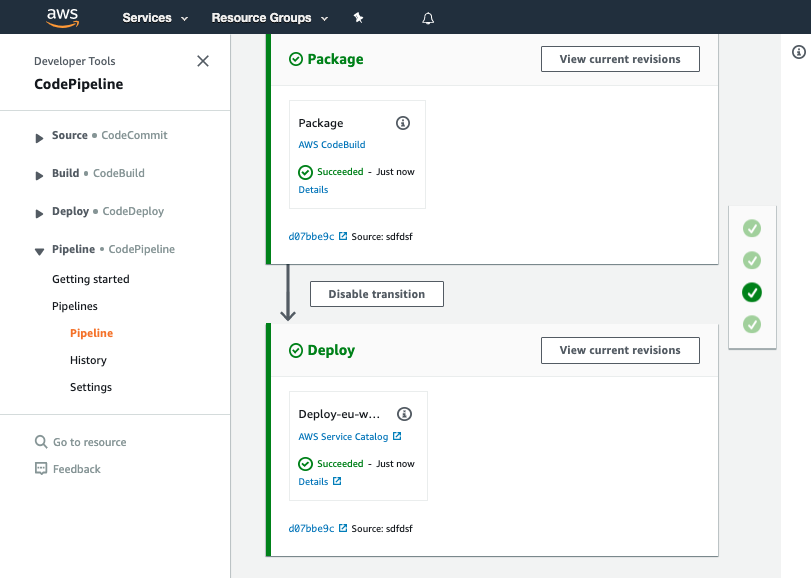
You should see your commit message on this screen, it will help you know which version of ServiceCatalogFactory repository the pipeline is processing.
If this is failing please raise your hand for some assistance
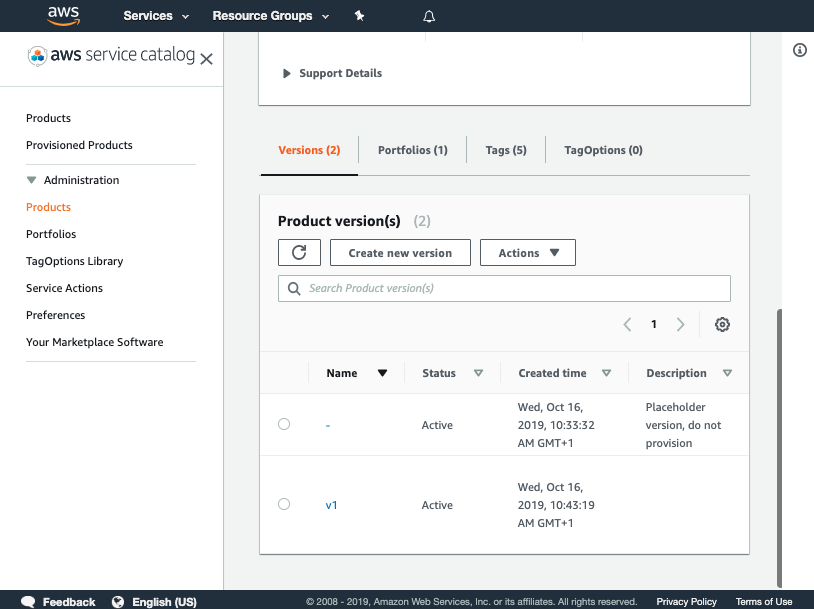
Once you have verified the pipeline has run you can go to Service Catalog products to view your newly created version.
You should see the product you created listed:
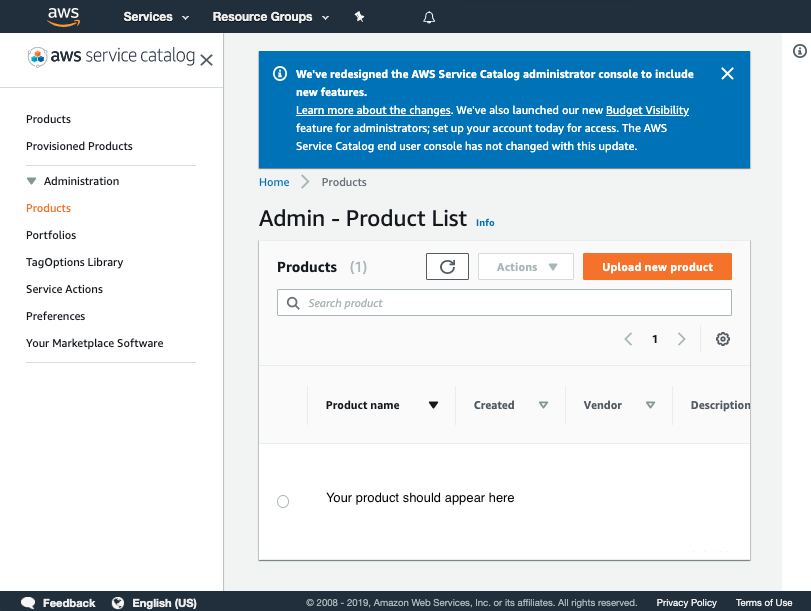
Click on the product and verify v1 is there
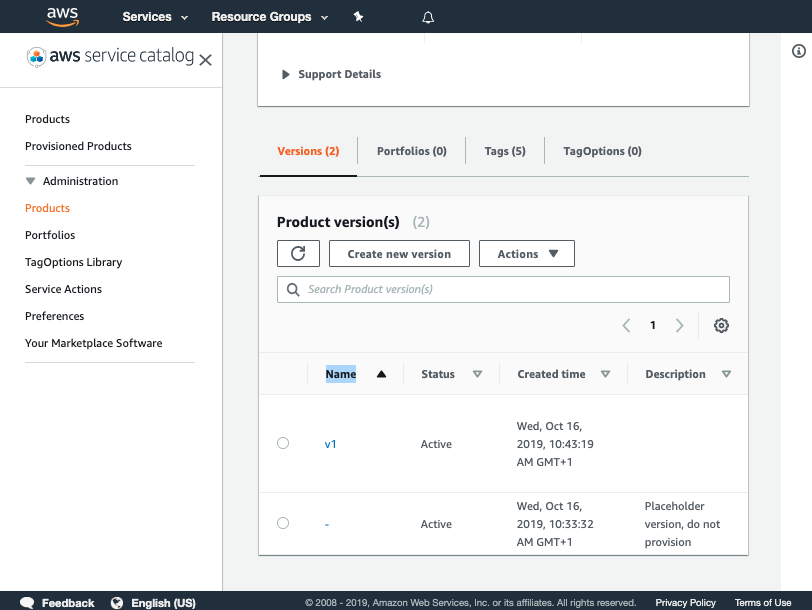
If you cannot see your version please raise your hand for some assistance
You have now successfully created a version for your product!
Verify the product was added to the portfolio
Now that you have verified the pipeline has run you can go to Service Catalog portfolios to view your portfolio.
- Click on reinvent-cloud-engineering-governance
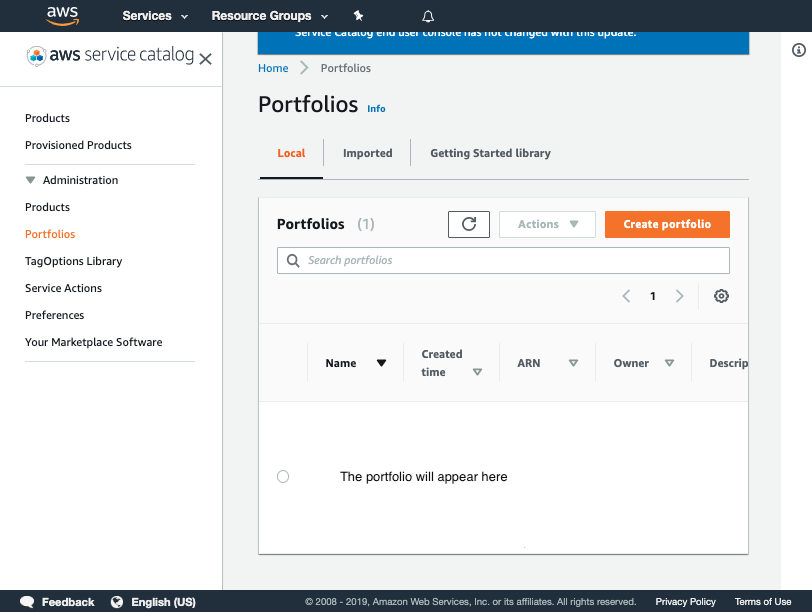
-
Click on the product aws-config-rds-storage-encrypted
-
Click on the version v1